Data security is being quietly eroded after "Cultured Crayfish" explodes in popularity
Recently, the open source AI intelligence OpenClaw (commonly known as the "little lobster" "lobster") suddenly burst into the red, the circle of friends, technical groups are in the sun "to raise the little lobster" skills: some people let it automatically organize the net, some people let it to take over the mailbox, the work order, the code base, and even directly to the business system to take over the power.
However, in just a few weeks, security alerts around "crawfish" have also appeared intensively: regulatory authorities have named some instances of serious security flaws in the default or improper configuration, which can easily induce cyberattacks and information leakage, and many universities and organizations have issued reminders or suspended the use of such instances.
While we are excitedly "raising lobsters", are we also surrendering our data sovereignty little by little?
Five Core Safety Hazards of Crawfish
Summarizing recent public notifications and expert analysis, the main risks surrounding "Crawfish/OpenClaw" are now broadly focused on five aspects:
1. Explicit Exposure and Weak Privilege Configuration
o Many users directly use the default configuration, exposing the “lobster” to the public network. Anyone can try to connect to this “naked lobster” by simply scanning it and read chat logs, account credentials, API keys and other sensitive information.
o Lack of fine-grained access control, “if you can connect, you can see everything” is like putting a “digital house key” on a neighborhood bulletin board.
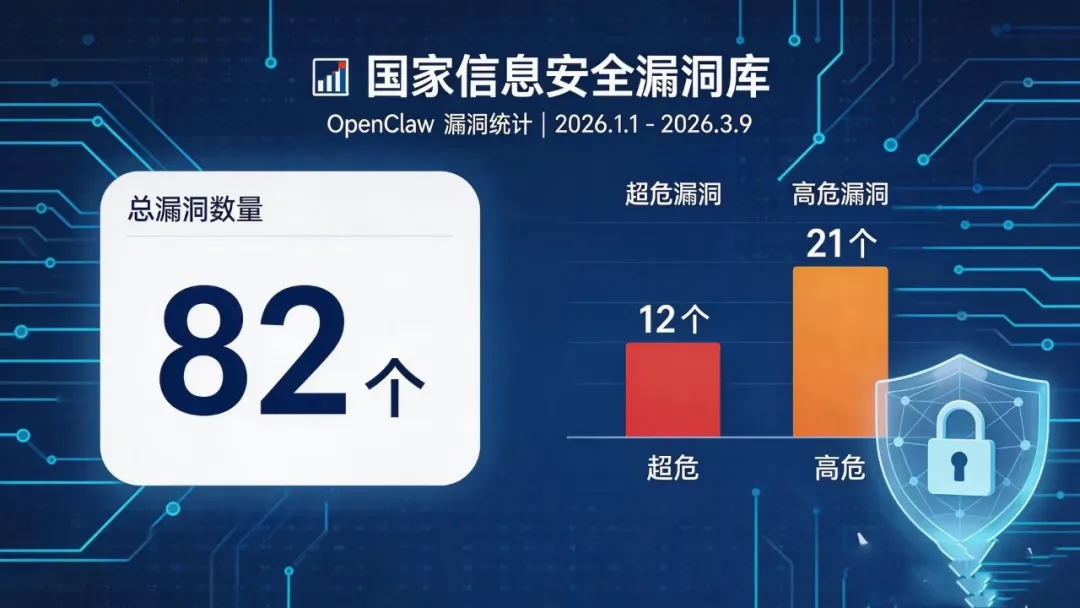
2. High-risk vulnerabilities and untimely updates
o The National Vulnerability Database has collected a large number of security vulnerabilities related to OpenClaw in a short period of time, many of which are of ultra-hazardous and high-risk levels, which, if exploited, could lead to remote control of the system or bulk data theft. o The National Vulnerability Database has also collected a large number of security vulnerabilities related to OpenClaw, many of which are of ultra-hazardous and high-risk levels.
o Many individuals and SMEs do not upgrade for a long period of time after deployment, resulting in “zombie instances” that become “long-term minefields” in the eyes of attackers.
3. Plug-ins and skill pack poisoning
o There are a large number of third-party skill packs and plug-ins in the Crawfish ecosystem, which lacks strict auditing and signing mechanisms. news+1
o Once a user installs a plug-in that has been implanted with malicious code, Lobster may silently package your files in the background, upload database backups, and even modify business information.
4. Misoperation due to autonomous execution capability
o As a locally operating intelligence with the ability to call on system resources, Lobster can perform high-risk operations such as deleting, moving, and renaming. o As a locally operating intelligence with the ability to call on system resources, Lobster can perform high-risk operations such as deleting, moving, and renaming. bjnews+1
o When commands are misunderstood or lured by malicious prompts, it may delete critical files, overwrite setup files, or even empty an entire hard disk without the user's knowledge.
5. Blurred boundaries of trust and unclear responsibilities
o Personal developers, installation services on behalf of the rampant, "who configured it," "who audited it," and "who is responsible for what happened" is often unclear. news+1
o For organizations, this means compliance risk: customer data and employee privacy can be compromised through Crawfish at a cost far greater than the price of a single server.
Simply put, “raising crayfish” itself is not an original sin, but in the absence of a secure framework and encrypted storage, a large amount of data is being handed over to a highly authorized, under-audited and ecologically mixed intelligence to “play freely”, and the risk naturally rises.
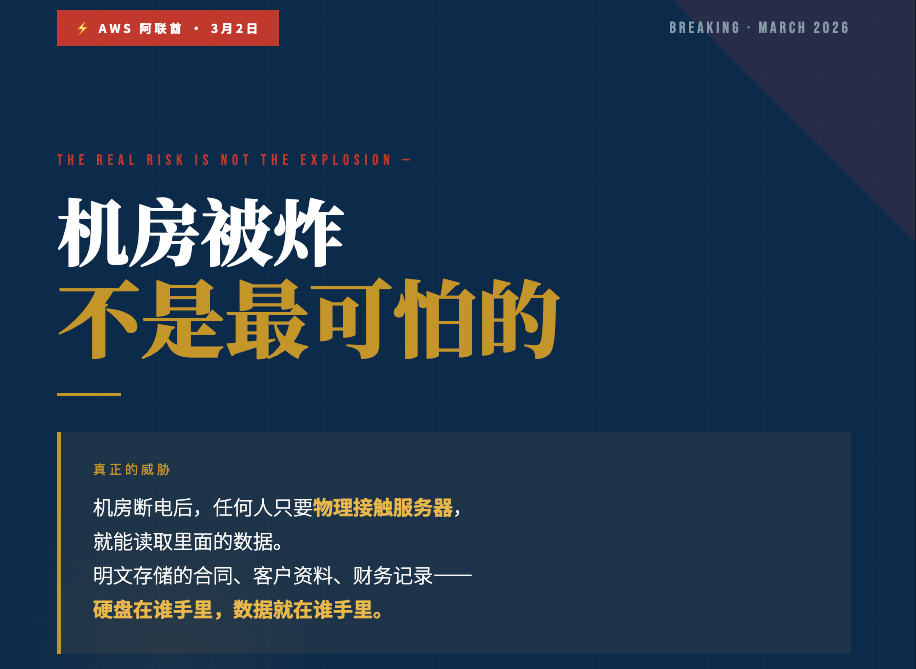
The really fatal problem: the data was never "quantum-level" protected in the first place.
This “crawfish incident” exposes not only the vulnerability of a tool, but also a common blind spot in the entire digital era: we focus on “whether it is good or not”, but often ignore the “storage security or not! ”The
If the enterprise's data is stored in an independent encrypted space like a digital vault from the beginning, there are at least three key defenses even if the "Little Lobster" is misconfigured or the plug-in is poisoned:
1. Physical isolation and dedicated space
o Dedicated space, starting at 3TB, is realized through independent storage units, completely isolating critical data from the general application tier, making it difficult for attackers to reach the data base even if an application instance is compromised.
o To the "crawfish", it sees only the controlled data interface, not the bare file system.
2. quantum level encryption and hierarchical key management
o The Digital Gold Platform (DGP) utilizes quantum-level encryption at the bottom of the platform for full lifecycle encryption management of stored data, and prevents key misuse through an independent key management system.
o Even if an attacker gains partial access at the system level, it is still difficult to restore plaintext data without a key, reducing the chance of large-scale data leakage.
3. Granular Authorization and Audit Closures
o Define "who accessed what data, when, in what context, and how" through the dimensions of roles, strategies, and scenarios, and keep complete audit logs. o Define "who accessed what data, when, in what context, and how" through the dimensions of roles, strategies, and scenarios, and keep complete audit logs.
o When an intelligent entity such as "Crawfish" is accessed, it can be restricted to access only specific data sets and specific interfaces, so that it can be quickly traced back and frozen in the event of abnormal access behavior.
In other words, if "Little Lobster" is a highly capable but immature intern, what the enterprise really needs is to set up the "treasury" and the "cashiering process" first, and then consider which tasks to let it participate in, instead of just dumping the safe key to it.
How do you get the "crayfish" to work for you instead of being "eaten up"?
For individuals and enterprises that are already using or planning to use AI intelligences such as Crayfish, we recommend reorganizing security thinking at three levels: data, application, and ecosystem.
1. Fixing the data base first: on the “vault”, then on the smart body
- Migrate or mirror core data into a digital vault with independent storage units and quantum-level encryption capabilities, with dedicated space to host business-critical data.
- Intelligence-oriented controlled data interfaces (APIs/encrypted computing interfaces), rather than direct database or file system paths, reduce the attack surface from the ground up.
2. Re-authorization: Intelligent entities can only “see what they should see”.”
- Create specialized roles for Crawfish, granting only the minimum permissions needed to complete a specific business, to avoid "one-size-fits-all read/write for the whole library".
- Configure different data views for different business scenarios, such as “customer service view”, “operation view” and “analysis view”, in the Digital Gold Platform. Intelligence only connects to the corresponding views, not to the original database tables.
3. Final ecological security supplement: backing up with auditing and encrypted computing
- Continuous recording and auditing of the intelligence's access behavior, with automatic alerts for abnormal patterns (large-scale export within a short period of time, frequent access to high-sensitivity meters, etc.).
- When it comes to analyzing highly sensitive data, the results are exposed through encrypted calculations, query desensitization, etc., instead of plaintext data, so that the intelligent body can “use the data” but try not to “see the data” as far as possible.
Under this framework, “raising crawfish” is no longer about stuffing data into a black box, but about making it a replaceable and upgradeable “smart plug-in” that really works around a secure data base.
Digital Vault: Reconstructing Data Ownership for the AI Era
From cloud computing to big models to today's intelligences, each wave of technology puts forward higher requirements for data security: data is no longer just a passive “asset”, but a “factor of production” that is constantly moving, being calculated and traded.
The Digital Gold Platform (DGP) is designed around this trend: it integrates the core capabilities of secure data storage, multi-data transactions, crypto-computing, and blockchain to provide one-stop data management services as a "digital vault" for individuals and enterprises.
- For individuals, it is both an “encrypted disk” and a gateway to future data asset realization, helping you to enjoy AI services while maintaining your privacy and sovereignty.
- For enterprises, it is a cross-departmental, cross-system data pedestal and security hub that supports data collaboration and value release under compliance without the risk of explicit text flying around.
AI intelligence will continue to evolve, and there will be “crabs” and “whales” after “crayfish”, but no matter how the shape changes, what will not be outdated is a set of cryptographic storage as the core of a future-oriented digital treasury system. The real thing will not be outdated is a set of cryptographic storage as the core, future-oriented digital treasury system.
If you're worried about the safety hazards of 'crawfish', ask yourself a question first:
Is your “digital vault” ready before any AI touches your data?
To find out how DVT Digital Vault can protect your business data, you are welcome to scan the code and join our consultant on WeChat, we will reply you within 24 hours.

Book a free trial - no sales pressure - one-to-one answers from professional consultants
DVT Digital Vault - Over 20 years of chip-level encryption technology to accumulate data sovereignty, starting now.








估計損失高達-19-億英鎊,為英國歷來之最.jpg)