The state of Nevada has released an extremely rare and transparent security incident investigation report detailing the complete attack process, detection and recovery actions of the August 2024 ransomware breach of state government.
The incident affected more than 60 government departments and caused widespread disruption to websites, telephone systems and many online services for citizens. It is worth noting that the State of Nevada did not pay the ransom and restored 90%'s critical systems within 28 days.
The case is highly transparent and is one of the rare cases where the government has taken the initiative to publicize the complete attack chain record, which is an important warning to all public sectors, technology enterprises and critical infrastructures.
Source of the attack: A Google advertisement as a breaching gap
According to the report, the attackers initially gained a foothold on the intranet on May 14, and the source was not a system vulnerability or a phishing email, but rather:
An information technology (IT) user clicked on a fake website directed by a malicious advertisement to download a backdoor system administration tool from a Google search tool.
This type of attack is called:
Malvertising (Malvertising Infection Chain)
In recent years threats have often masqueraded as popular IT tools, such as:
WinSCP, PuTTY, KeePass, AnyDesk, LogMeIn
The target is not the average user, but the system administrator with high privileges.
Attackers use this to gain direct access to key portals for lateral movement and privilege escalation.

The key breaking point is the successful invasion of the attacker:
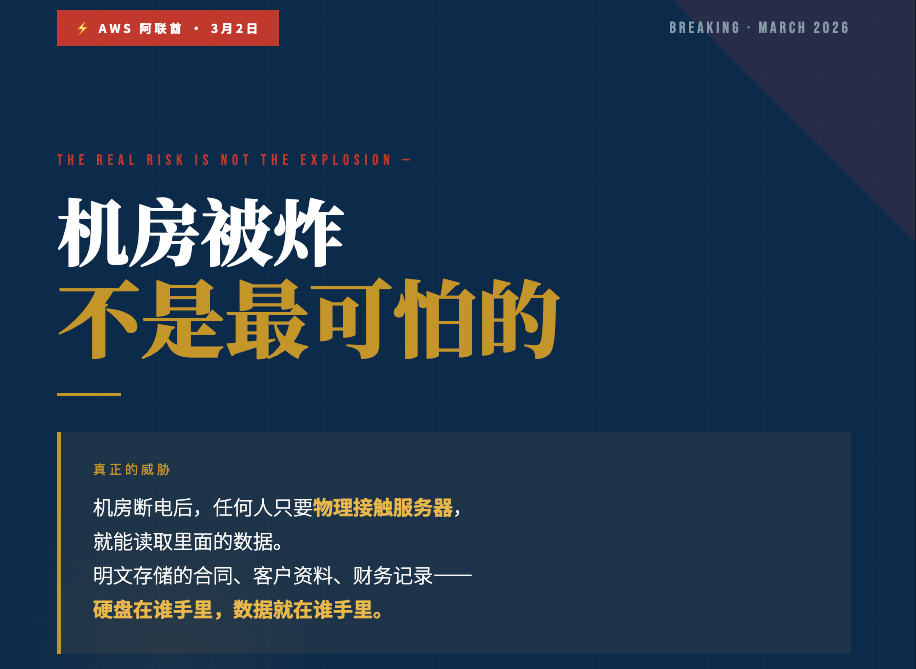
Password Vault System
Theft of 26 sets of high-authority account credentials
Let them be:
- Log in to the core server
- Clearing event logs (hidden traces)
- Further deployment of ransomware
August 24, 08:30 (UTC) / 16:30 HKT
The ransomware was fully activated and the Nevada State Government's virtual machine server farms were encrypted simultaneously, bringing the system to a complete standstill.
Why did you refuse to pay the ransom? "I'd rather pay overtime than give the hackers a dime."
Nevada chose not to negotiate and pay the ransom instead:
- Activation of the Established Information Security Response Playbook (Incident Response Playbook)
- 4,212 hours of overtime work by 50 in-house staff
- Completion of system restoration at $259,000 overtime
If it were to be outsourced, the mark-to-market cost would be higher by about US$478,000.
During the incident, the authorities still ensured that:
Civil service payroll was normalized, public safety communications were uninterrupted, and services to the public were gradually resumed.
Incident reveals three major security revelations
- Organizations must develop an "assumed breached" security mindset.Even if endpoint antivirus detects the backdoor, the attacker can still maintain persistent access. → Zero-trust architecture, continuous monitoring, and honeypot detection must be in place.
- Password vaults and privileged accounts are at the center of attacks and defenses.Once an attacker gains access to the password database, he or she can bypass all boundary defenses. → Password libraries, Active Directory, and Identity Access Management (IAM/PAM) are the primary points of defense.
- Backup mechanism cannot rely solely on the backup itselfDeletion of a backup stalls recovery. → Backups should be isolated offline, stored in immutable storage, and the recovery process should be rehearsed regularly.
Conclusion: Transparency as a model of best practice in security governance
The value of this Nevada report is this:
No cover-ups, no whitewashing, full disclosure of every step of the attack.
This is not just a system recovery, it's a one-off:
A successful demonstration of organizational Cyber Resilience,
It is an important example of building trust between the Government and the community,
A resource for all corporations and public organizations on information security governance.
In the face of the increasingly mature ransomware ecosystem, the industry needs to be more:
faster detection capabilities, better identity rights management, and more stringent redundancy strategies.
And a more realistic and unapologetic culture of after-action review.
Source:
https://blog.billows.com.tw/?p=3990%EF%BC%89








估計損失高達-19-億英鎊,為英國歷來之最.jpg)
