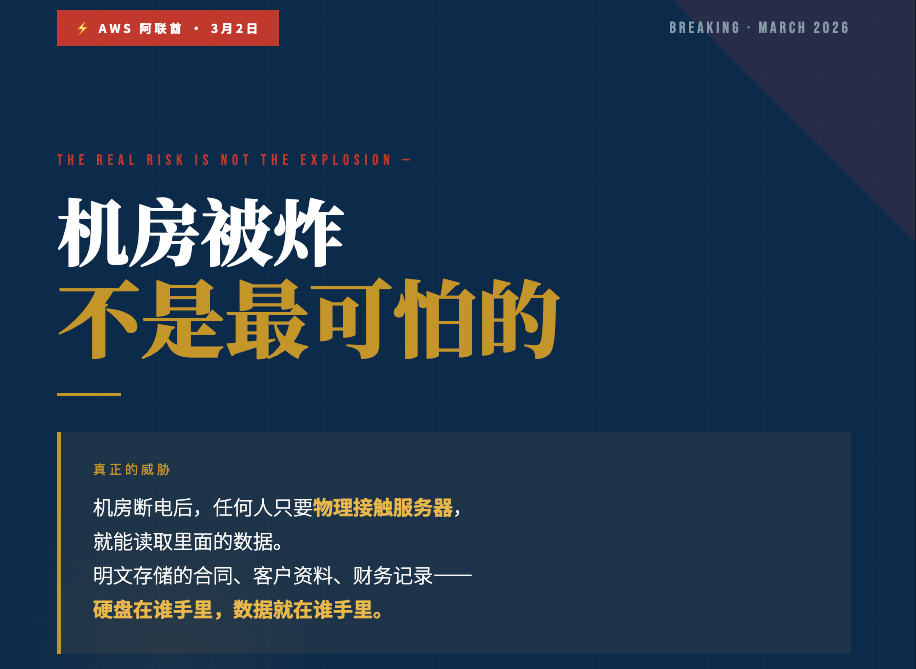
On March 2, a drone hit the Amazon AWS data center in the United Arab Emirates, paralyzing the apps of several banks in Dubai and disrupting corporate data for more than 24 hours. It's worth thinking about for every business owner who leaves their data in someone else's hands.
First, the disconnection is only the first problem.
The first reaction of many people who saw this news was:
“Good thing I'm not in the Middle East.”
However, disconnection is actually the smallest problem.
After the power went out in the AWS server room, rescuers, engineers, and even those who took advantage of the chaos to enter the scene-anyone who physically touched the server hardware had the opportunity to read the data inside.
Why?
This is because the vast majority of enterprise data that exists in the cloud is stored in plaintext.
The meaning of plaintext storage is simple: your contracts, your customer lists, your financial records are raw files that can be read directly on the server. Whoever has the hardware has the data.
This is not a problem unique to AWS.
This is the default storage method for the entire industry.
Second, a question you may not have thought about.
Where is your data now?
Whether it's AliCloud, Tencent Cloud, Google Drive, or a company NAS-ask a question:
If someone took the hard drive with your data on it tonight, what could he see?
If the answer is ”I can see everything,” then you're not inherently at risk in the same way as the organizations in the AWS Emirates server room.
Physical attacks are an extreme case.
The more common threat is:
Vulnerable Access by Service Provider Insiders
Batch export after hackers get access to server admin rights
Account Privileges Taken by Exiting Employees
Transmission Interception during Data Migration
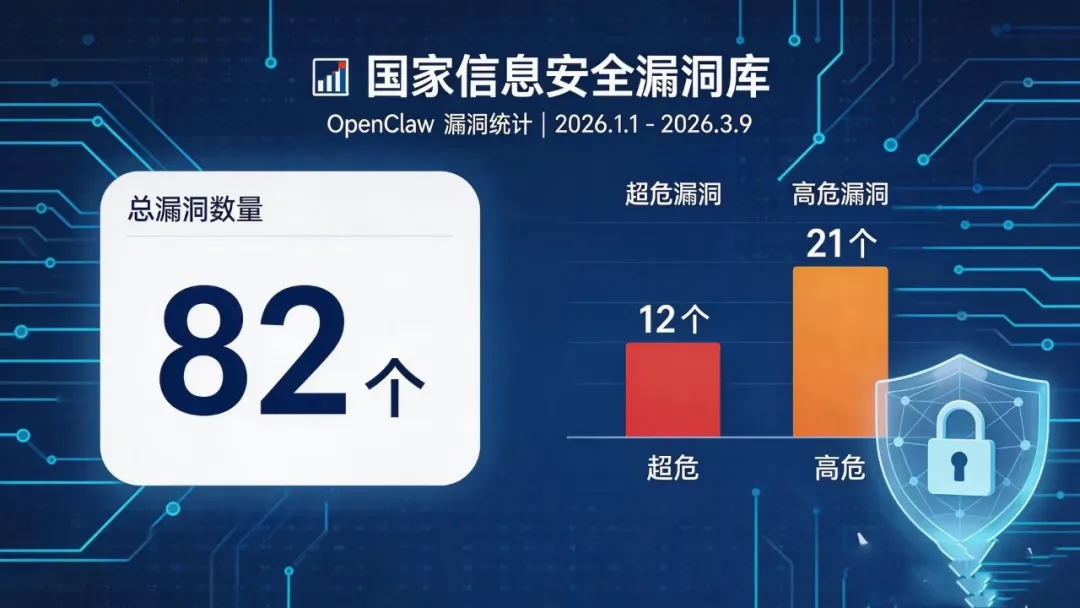
These things happen every day. It's just that most businesses don't realize it until 287 days later.
287 days. This is the average time it will take for a global business to discover a data breach in 2025.
By that time, your customers' information may already be circulating on the dark web.
III. Encryption, not optional
When many business owners hear ”data encryption”, their first reaction is:
“We're small enough that no one should be targeting us.”
However, small and medium-sized enterprises (SMEs) accounted for the vast majority of data breaches.
The reason is simple: SMEs are the easiest targets because of their thin defenses and low attack costs.
Hong Kong formally implemented the Protection of Critical Infrastructure (Computer Systems) Ordinance in January 2026, and data security regulatory efforts in the Greater Bay Area continue to be strengthened.
In addition to the pressure of compliance, a more realistic problem is: once the customer data leakage, the loss of not only fines, is the trust. And trust is the most difficult thing for SMEs to rebuild.
What is true data security?
Let us talk about a specific incident.
The logic of the DVT Digital Vault is this:
Your data is encrypted at the hardware level by your proprietary A5 chip before it enters the server room.
What's stored in the computer room is a secret message.
Not your original contract, not your customer data, not your financial data - it's encrypted cipher text that no one can read directly.
And the key to decryption - the UKey physical key - is in your hands.
Not in the hands of the service provider. Not in the cloud. Not in any third-party system.
In your hand.
What does that mean?
Even if the server room suffered a physical attack, even if hackers got their hands on the server's administrative privileges, even if the hard drives were taken right out of the box-
Without your UKey, all you get is a bunch of random code that no one can read.
A piece of scrap metal.
AWS Bombed News, Soon to Disappear from Top Searches.
But the risks to data security will not disappear just because the news goes cold.
We are not writing this article to peddle fear.
Rather, it's because, in a large number of corporate cases we've seen, the moment something goes wrong, the first thing everyone says is:
“I didn't think it would be my turn.”
Now is a good time to think seriously about this.
To find out how DVT Digital Vault can protect your business data, you are welcome to scan the code and join our consultant on WeChat, we will reply you within 24 hours.

Book a free trial - no sales pressure - one-to-one answers from professional consultants
DVT Digital Vault - Over 20 years of chip-level encryption technology to accumulate data sovereignty, starting now.








估計損失高達-19-億英鎊,為英國歷來之最.jpg)